Do you really need to take email security seriously? Maybe. How much effort to invest in encrypting and securing an email depends on several factors including your personal situation and which parts of the communication need to be secured. Before deciding which options are right for you it helps to first understand all of the components involved in the process, the vulnerabilities, and any special requirements. The following diagram is a high-level overview that shows, from left to right, the path a typical email takes from the sender to the final recipient:
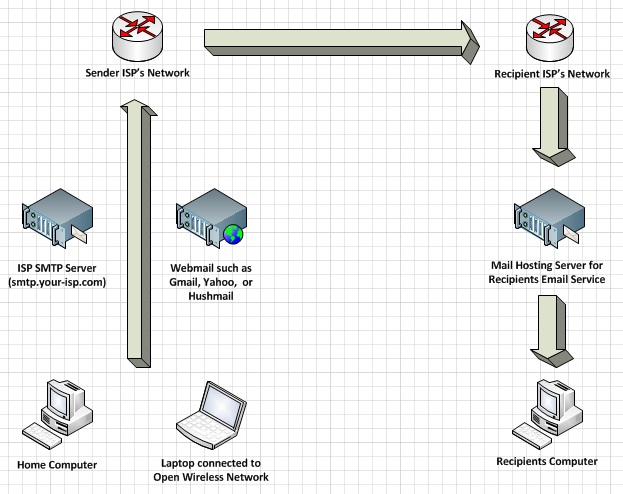
Most of the major free webmail providers such as Gmail, Hotmail, and Yahoo Mail support secure connections. Users who send and receive email through their ISP (Internet Service Provider) from a program on their computer will need to check if their ISP supports pop3+ssl on port 995 and smtp+ssl most often on ports 25 or 587; for example, how to check your Thunderbird email settings. When sending an email using a free webmail account or through your ISP's mail servers, it's important to keep in mind that the actual email is not encrypted; only the connection between your computer and their servers, along the left arrow above, will be secured. Most of the time, it is possible for a 3rd party, along the right and down arrows, to read your email after it is sent.
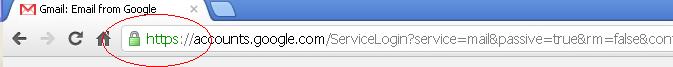
In addition to the email itself not being encrypted, using the above services, such as Yahoo Mail expose you to additional risk when on a public wireless network. While Gmail and Hotmail use full session HTTPS, which means that all pages between your computer and their webmail applications are encrypted, Yahoo Mail only encrypts user login pages. This means that your email could be captured by someone who is also connected to the same wireless network when sending. For more information on these and related issues please read our top 5 tips on preventing your email from getting hacked.
As the owner of a small company, I find that securing sensitive email attachments is one of my greatest email concerns. I am often required to send emails with attachments that contain my social security number and other personal information. To limit the number of systems that these attachments are sent through, I use a service called Hushmail to send encrypted attachments. First I zip and password protect the file by right clicking and compressing with 7-zip, then I compose a new email using my Hushmail account and attach the encrypted file before sending. Instead of sending the email with file attachment to the recipient, Hushmail sends them an email notice to let them know that there is a secure download waiting for them. Knowing the answer to my secret question for that email, they can then access and download the email and attachment with their web browser. I feel this is more secure since the attachment has not passed through several mail servers, is not saved in a sent mail folder, it is not archived in the recipients mail program, and can be deleted from my computer after sending. Using Hushmail also makes it easy for me to email attachments without needing extra configuration on my home computer such as security software or personal certificates.
Although the well known 3rd party services such as Hushmail are generally safe, they might not be approved for use by employees within a larger corporation. In this case the company could add a plugin to Microsoft Outlook to enable sending encrypted email attachments. Certain employees may also want to encrypt all emails sent by Microsoft Outlook. There is more configuration involved with this setup than in the Hushmail scenario above, but it's likely more appropriate for corporate employees. Corporate employees may want to contact their IT Help Desk or Security Team for current supported options and best practices within their company.
I'm sure you've heard it before, but common sense is still one of the best ways to protect your email accounts. Never reply to phishing emails asking you to confirm your account details or other personal information, and never open unexpected email attachments even from people you trust.
- Are you a home user primarily concerned with protecting your password?
- Do you connect to the open wireless network at your favorite coffee shop?
- Is there a need for you to secure your email conversations?
- Do you need to send encrypted email attachments?
Most of the major free webmail providers such as Gmail, Hotmail, and Yahoo Mail support secure connections. Users who send and receive email through their ISP (Internet Service Provider) from a program on their computer will need to check if their ISP supports pop3+ssl on port 995 and smtp+ssl most often on ports 25 or 587; for example, how to check your Thunderbird email settings. When sending an email using a free webmail account or through your ISP's mail servers, it's important to keep in mind that the actual email is not encrypted; only the connection between your computer and their servers, along the left arrow above, will be secured. Most of the time, it is possible for a 3rd party, along the right and down arrows, to read your email after it is sent.
In addition to the email itself not being encrypted, using the above services, such as Yahoo Mail expose you to additional risk when on a public wireless network. While Gmail and Hotmail use full session HTTPS, which means that all pages between your computer and their webmail applications are encrypted, Yahoo Mail only encrypts user login pages. This means that your email could be captured by someone who is also connected to the same wireless network when sending. For more information on these and related issues please read our top 5 tips on preventing your email from getting hacked.
As the owner of a small company, I find that securing sensitive email attachments is one of my greatest email concerns. I am often required to send emails with attachments that contain my social security number and other personal information. To limit the number of systems that these attachments are sent through, I use a service called Hushmail to send encrypted attachments. First I zip and password protect the file by right clicking and compressing with 7-zip, then I compose a new email using my Hushmail account and attach the encrypted file before sending. Instead of sending the email with file attachment to the recipient, Hushmail sends them an email notice to let them know that there is a secure download waiting for them. Knowing the answer to my secret question for that email, they can then access and download the email and attachment with their web browser. I feel this is more secure since the attachment has not passed through several mail servers, is not saved in a sent mail folder, it is not archived in the recipients mail program, and can be deleted from my computer after sending. Using Hushmail also makes it easy for me to email attachments without needing extra configuration on my home computer such as security software or personal certificates.
Although the well known 3rd party services such as Hushmail are generally safe, they might not be approved for use by employees within a larger corporation. In this case the company could add a plugin to Microsoft Outlook to enable sending encrypted email attachments. Certain employees may also want to encrypt all emails sent by Microsoft Outlook. There is more configuration involved with this setup than in the Hushmail scenario above, but it's likely more appropriate for corporate employees. Corporate employees may want to contact their IT Help Desk or Security Team for current supported options and best practices within their company.
I'm sure you've heard it before, but common sense is still one of the best ways to protect your email accounts. Never reply to phishing emails asking you to confirm your account details or other personal information, and never open unexpected email attachments even from people you trust.
Last edited:
